ASUS™ AiProtection reports suspicious networking behavior from TellStick
Some users have been reporting their (ASUS™) routers reports suspicious networking behavior from TellStick. The router alerts that TellStick tries to connect to a suspicious server on the internet.
The alert looks similar to this:
Alert type : Infected Device Prevention and Blocking Source : (AC:CA:54:XX:YY:ZZ) Destination : 193.11.114.43 RT-AC87U’s AiProtection detected suspicious networking behavior and prevented your device making a connection to a malicious website
These types of reports should always be treated seriously. It could be a sign that one of your devices on your network is infected with a malware.
tl;dr
If you aren't interested in the technical description below you can safely ignore this warning. The warning is a false positive.
The technical…
Upon inspection of the captured packets, the IP address reported (193.11.114.43) was not found in the communication of the gateway and the Internet, suggesting the infected source was not on the gateway.
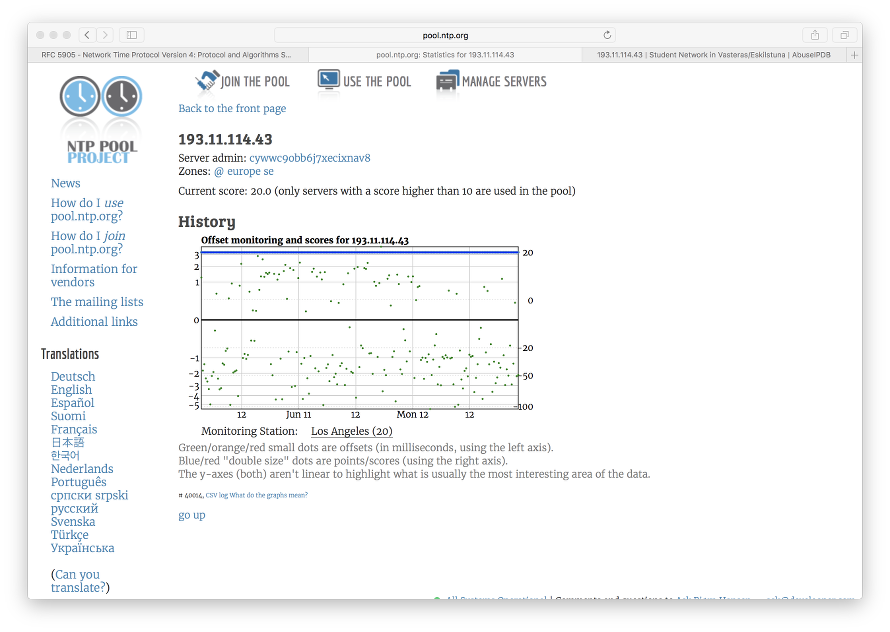
Upon further inspection on the frequent traffic, it was found that NTP accounted for most of the traffic when the gateway is in idle mode. Cross checking with the search results on Google on this IP address indicated it once belonged to the pool of NTP servers under pool.ntp.org.
Querying the IP address via NTP Statistics confirms this IP address was indeed part of the ntp pool machines.
However, a reverse DNS lookup on the same IP yielded a different domain name: tor1.msfnet.se.
root@mangocrap:/var/lib/misc# nslookup 193.11.114.43 Server: 192.168.1.1 Address: 192.168.1.1#53 Non-authoritative answer: 43.114.11.193.in-addr.arpa name = tor1.mdfnet.se. Authoritative answers can be found from:
A DNS lookup in tor1.msfnet.se however revealed no associated IP address,:
root@mangocrap:/var/lib/misc# nslookup tor1.mdfnet.se Server: 192.168.1.1 Address: 192.168.1.1#53 ** server can't find tor1.mdfnet.se: NXDOMAIN
suggesting this is a stale record of the reverse DNS lookup.
The ASUS AiProtection works by querying a third party service (WRS database provided by Trend Micro™) on a suspicious IP address to determine if it is a malicious host.
Looking from this case, it is reasonable to believe either ASUS or Trend Micro uses reverse DNS lookup for the domain name and match it with the list of malicious hosts. In practice, since domain names can be binded to different IP addresses at different time intervals, the IPS mechanism shall not only rely on domain names but also verify using the IP address for malicious host detection in order to reduce false positives.
In conclusion, the IP address that was associated with a malicious web site was being reused as one of the NTP machines in pool.ntp.org for serving network time, the reverse DNS lookup still shows that IP address is being associate with the malicious web site, thus triggering a false positive in the AiProtection mechanism, resulting in the security alert given from the ASUS router. To mitigate, suggest user to report to ASUS on this false positive, and if the router have a whitelist function, add this IP address to the whitelist so that the router will stop generating alerts for this IP address.
Lua-script for sirens
We've just pushed Lua scripts to enable controlling different sounds on the sirens from AeonLabs, CoolCam and Philio (and also D-Link that is same device as Philio) from dummy devices. The siren()-function can of course be used in other ways as well.
https://github.com/telldus/tellstick-lua-examples/blob/master/zwave/AeonLabs/Siren.lua
https://github.com/telldus/tellstick-lua-examples/blob/master/zwave/CoolCam/Siren.lua
https://github.com/telldus/tellstick-lua-examples/blob/master/zwave/Philio/Siren.lua
 rss
rss